Note: Need help with DirectAccess troubleshooting? Use the contact form at the end of this post to request assistance!
To aid in troubleshooting Windows DirectAccess client configuration and connectivity, Microsoft recently made available the Windows DirectAccess Client Troubleshooting Tool. The tool, which is a portable executable based on the .NET Framework and does not require installation, operates by performing a series of tests and health checks on a connected DirectAccess client. As of this release, the troubleshooting tool checks network interface configuration, Network Location Server (NLS) reachability, IP connectivity and the status of transition technologies, Windows Firewall with Advanced Security configuration, computer certificate status, as well as network connectivity over the infrastructure and user IPsec DirectAccess tunnels.
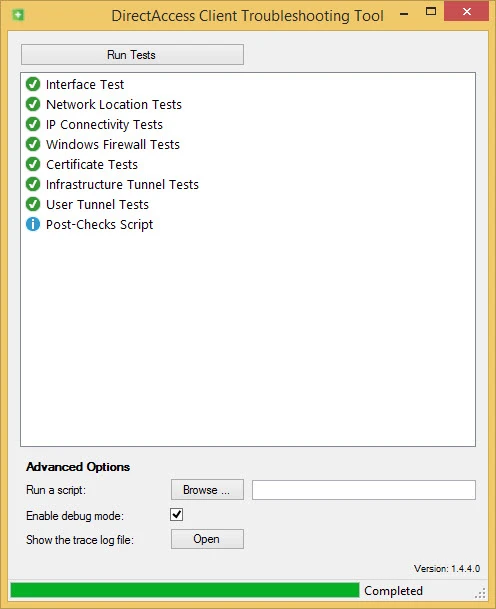
The tool also features an optional debug mode that provides highly detailed information gathered from each of the tests executed.

The tool is supported on both Windows 7 and Windows 8.x clients. If you implement or support DirectAccess, this utility will certainly speed up your troubleshooting by providing deep insight in to the configuration and current connectivity status for your DirectAccess clients. You can download the Microsoft DirectAccess client troubleshooting tool here.
Additional Resources
Planning and Implementing DirectAccess with Windows Server 2016 on Pluralsight
Implementing DirectAccess with Windows Server 2016 Book
Need Help with DirectAccess Troubleshooting?
If you’d like some help with your DirectAccess troubleshooting efforts, feel free to drop me a note! Fill out the contact form below and I’ll get in touch with you.













